Abstract:
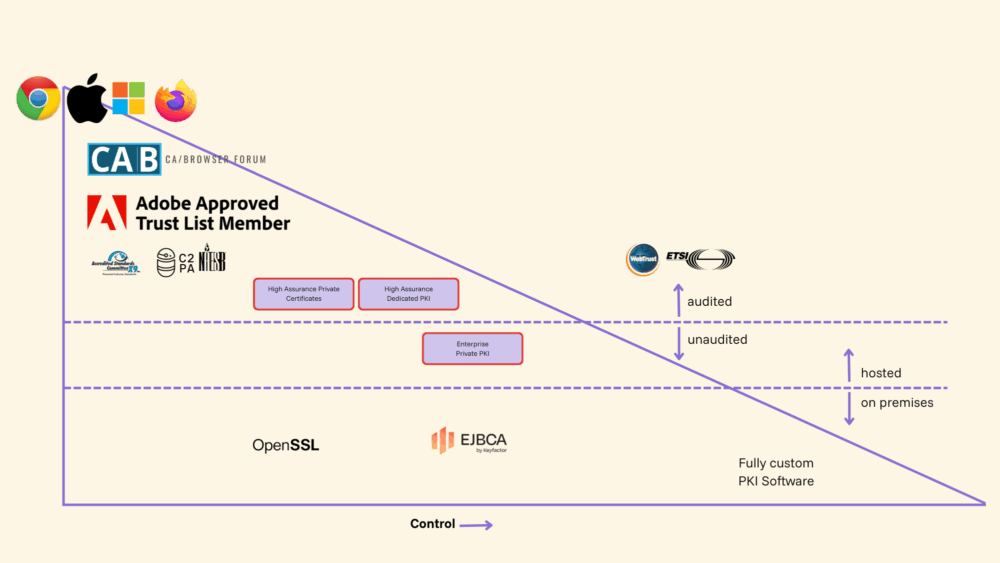
Most organizations secure their public-facing websites with digital certificates but overlook vital internal infrastructure, such as VPNs, device networks, and DevOps pipelines. Private PKI closes that gap by letting you issue and manage certificates on your own terms with custom profiles, flexible lifetimes, and no CT logging, which reveals details on your internal networks. SSL.com now offers three hosted Private PKI options to fit any organization’s needs.
Your company website has a digital certificate. Your email is encrypted. Your checkout page shows that reassuring little padlock.
But what about everything else?
The internal networks your teams rely on daily, the VPN your remote workers connect through, the hundreds of devices your IT department manages, the DevOps pipelines pushing code to production? If you’re like most businesses, you might be securing your public-facing front door while leaving the hallways and back rooms wide open. That’s the gap private public key infrastructure was built to close.
Contact Us Now for Private PKI Solutions
What Is the Difference Between Public and Private Public Key Infrastructure (PKI)?
Public Key Infrastructure (PKI) is the system that issues and manages digital certificates—the credentials that enable encryption, authentication, and secure communication across your organization.
But there are two fundamentally different models:
Public PKI
Public PKI secures internet-facing websites. Certificates are issued by publicly trusted Certificate Authorities (CAs) whose root CA certificates are embedded in browsers like Chrome, Safari, and Firefox.
This is essential for:
- Public websites
- E-commerce
- Customer-facing portals
However, public PKI comes with rules (such as CA/Browser Forum requirements) that limit certificate lifetimes and algorithms, and those certificate lifetimes are shrinking. Certificate content is tightly regulated. And every digital certificate you issue through a public CA gets logged in public transparency records. While that’s what makes the public web trustworthy, this also presents a certain degree of operational risk.
Private Public Key Infrastructure (Private PKI)
A private PKI (sometimes referred to as a private or internal CA) operates under your organization’s trust model rather than the public internet’s. Instead of relying on browser root stores, you control (or delegate control of) your own private CA hierarchy.
For you, this means:
- Greater flexibility
- Custom certificate profiles
- Control over certificate lifetimes
- Policies tailored to your infrastructure
A private CA lets your organization issue digital certificates for internal use without the constraints of public trust policies. You control the certificate profiles, lifetimes, the security controls, and who gets access. Nothing gets logged publicly because these certificates aren’t meant for the outside world; they’re only for use within your organization.
Private PKI Use Cases and Benefits
Here are the most common scenarios where organizations turn to private PKI:
Securing remote access – VPN connections and Wi-Fi authentication are far more secure when backed by certificate-based identity rather than passwords alone. A private CA lets you issue certificates to authorized users and devices, so only the right people can access them.
Managing devices at scale – Whether it’s laptops, mobile phones, or IoT endpoints, mobile device management (MDM) systems work best when every device carries a trusted certificate. Issuing certificates through a private PKI makes enrollment seamless and revocation instant.
Protecting internal services – Mutual TLS between microservices, encrypted traffic across data centers, secure staging environments — these are all internal concerns that don’t require public trust but absolutely need strong encryption and authentication.
Accelerating DevOps – Development and CI/CD pipelines need certificates too, often with fast turnaround and non-standard configurations. Private PKI gives DevOps teams the flexibility to automate certificate issuance without bumping into public trust limitations.
Public CAs are optimized for internet-facing services. They are not designed for:
- Internal hostnames
- Test/staging environments
- East-West traffic secured with mutual TLS
- Device authentication at scale
- Custom certificate policies
- Long-lived infrastructure roots
How SSL Makes Private PKI Accessible
SSL now offers three Private PKI options to server organizations of all sizes. Our team can provide your organization with a fully hosted Private PKI solution, complete with self-service instant CA creation, API-based enrollment, optional ACME, OCSP, and CRL support:
High Assurance Private Certificates – A hybrid of public and private trust that includes customizable options and certificate issuance from WebTrust-audited Certificate Authorities.
High Assurance Dedicated PKI – Highly customizable, tailor-fit solution for large organizations with high compliance needs.
Enterprise Private PKI – General IT needs that do not require high compliance (i.e., mobile device management, VPN, internal networks, DevOps).
Public Trust vs. SSL’s Private PKI Options Technical Comparison
|
Public Trust? |
High-Assurance Private Certificates |
High-Assurance Dedicated PKI? |
Enterprise Private PKI? |
|
|
CA lifecycle ? |
Planned with key ceremonies and evidence gathering? |
Planned with key ceremonies and evidence gathering? |
Planned with key ceremonies and evidence gathering? |
Dynamic w/ self-service creation and removal ? |
|
Algorithms and key types/sizes? |
Limited by public trust requirements? |
Defined by Private PKI CPS? |
Limited by supporting infrastructure? |
Not limited? |
|
Certificate lifetime? |
Limited by public trust requirements? |
Defined by Private PKI CPS. Relaxed from CA/B limits? |
Limited by CPS defined jointly.? |
Not limited? |
|
Certificate content and profiles? |
Limited by public trust requirements? |
Defined by Private PKI CPS |
Limited by CPS defined jointly.? |
Not limited |
|
Verification requirements? |
Per public trust requirements? |
Defined by Private PKI CPS |
Optional, per CPS defined jointly. ? |
Not required |
|
Auditing assurance? |
WebTrust or ETSI? |
WebTrust? |
WebTrust? |
Not available? |
|
Network security standards? |
Per CA/B NetSec? |
Per CA/B NetSec? |
Per CA/B NetSec? |
High security + industry best practices? |
|
Security hardware? |
FIPS 140-3 or CC EAL4+? |
FIPS 140-3? |
FIPS 140-3? |
FIPS 140-3 |
Public vs. Private Trust
The Bottom Line
A private public key infrastructure offers you:
- Control without complexity
- Security without rigidity
- Compliance without operational friction
Almost every organization eventually reaches a point where public trust certificates alone aren’t enough. When your internal infrastructure, devices, and teams need the same level of cryptographic protection you provide to your website visitors, private PKI is the answer.
Ready to see what Enterprise Private PKI looks like for your organization? Talk to our PKI experts today.