Welcome to the October 2019 edition of SSL.com’s Security Roundup, an end-of-month digest where we highlight important developments in the field of SSL/TLS, digital certificates, and digital security.
On the browser front this month, Google has decided to start blocking mixed content in Chrome, and Mozilla Firefox has been named the most secure browser by Germany’s information security agency.
In other security-related news, Google’s Pixel 4’s Face Unlock system currently lacks an alertness check, Linux users should upgrade sudo, and Google researchers have published a paper in Nature detailing advances in quantum computing.
Google to Block All Mixed Content in Chrome
The Chromium blog announced on October 3, 2019 that Chrome will soon begin blocking all mixed content, a condition where subresources of an HTTPS website are loaded insecurely over HTTP. Up until this time, browsers have been blocking active mixed content such as scripts and iframes. Chrome will now begin to block passive mixed content (e.g. images, audio, and video), which also present security risks. For example,
an attacker could tamper with a mixed image of a stock chart to mislead investors, or inject a tracking cookie into a mixed resource load. Loading mixed content also leads to a confusing browser security UX, where the page is presented as neither secure nor insecure but somewhere in between.
Google’s move to block mixed content will take place in a series of steps beginning with Chrome 79 (stable release in December 2019) and continuing through Chrome 81 (early release in February 2020).
To avoid breaking the web insofar as possible, Chrome will attempt to automatically upgrade HTTP resources to HTTPS (if available), and users will permitted to enable mixed content on a site-by-site basis.
German Agency Names Firefox “Most Secure Browser”
An audit by Germany’s Federal Office of Information Security (in German, the Bundesamt für Sicherheit in der Informationstechnik, or BMI) has declared that Mozilla Firefox was the only browser tested that met the agency’s recently-updated minimum requirements to be considered sichere (pardon our Deutsche). According to ZDNet,
The BSI normally uses this guide to advise government agencies and companies from the private sector on what browsers are safe to use.
Tested browsers included Firefox 68, Chrome 76, IE 11, and Edge 44. ZDNet’s article also states that the tests “did not include other browsers like Safari, Brave, Opera, or Vivaldi.”
Stay Awake Around Your Pixel 4
As discovered by Chris Fox at the BBC, Google’s Pixel 4 smartphone has a Face Unlock system that “can allow access to a person’s device even if they have their eyes closed.” In contrast, Apple’s iOS Face ID does include an alertness check that makes sure that the user is awake and looking at the phone. For its part, Google says that it will fix the problem “in the coming months.”
Sudo Flaw Lets Users Run Commands as Root
An October 14 story in the Hacker News (thehackernews.com, not news.ycombinator.com) outlines a newly-discovered vulnerability in the commonly-used sudo command that “could allow a malicious user or a program to execute arbitrary commands as root on a targeted Linux system even when the ‘sudoers configuration’ explicitly disallows the root access.”
The security flaw, which depends on a specific configuration of the /etc/sudoers file, affects all versions of sudo prior to 1.8.28. It can be exploited by specifying the user ID -1 or 4294967295 on the command line.
Quantum Computing Breakthrough at Google
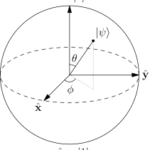
On October 23, researchers at Google published a paper in Nature, reporting that their new quantum processor, “Sycamore,”
takes about 200 seconds to sample one instance of a quantum circuit a million times—our benchmarks currently indicate that the equivalent task for a state-of-the-art classical supercomputer would take approximately 10,000 years.
However, a CBS news article indicates that some controversy surrounds the finding, with IBM researchers stating that Google had “underestimated the conventional supercomputer, called Summit, and said it could actually do the calculation in 2.5 days.” Possibly not coincidentally, Summit was developed by IBM.
Thank you for visiting SSL.com, where we believe a safer Internet is a better Internet! You can contact us by email at Support@SSL.com, call 1-877-SSL-SECURE, or just click the chat link at the bottom right of this page.


