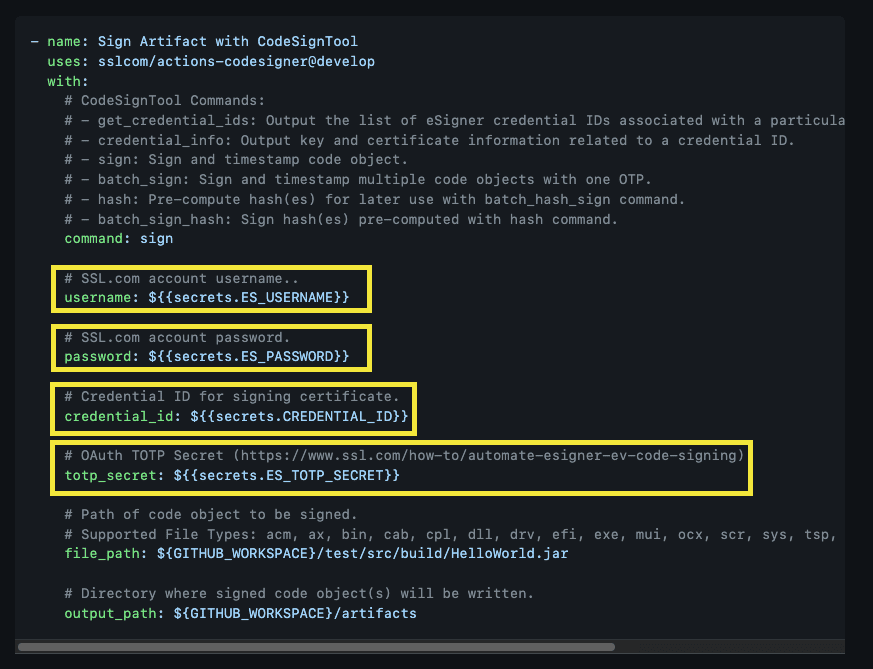
Usage
– name: Sign Artifact with CodeSignTool
uses: sslcom/actions-codesigner@develop
with:
- CodeSignTool Commands:
– get_credential_ids: Output the list of eSigner credential IDs associated with a user.
– credential_info: Output key and certificate information related to a credential ID.
– sign: Sign and timestamp code object.
– batch_sign: Sign and timestamp multiple code objects with one OTP.
– hash: Pre-compute hash(es) for later use with batch_hash_sign command.
– batch_sign_hash: Sign hash(es) pre-computed with hash command.
command: sign
- SSL.com account username.
username: ${{secrets.ES_USERNAME}}
- SSL.com account password.
password: ${{secrets.ES_PASSWORD}}
- Credential ID for signing certificate.
credential_id: ${{secrets.CREDENTIAL_ID}}
- OAuth TOTP Secret (https://ssl.com/how-to/automate-esigner-ev-code-signing)
totp_secret: ${{secrets.ES_TOTP_SECRET}}
- Path of code object to be signed.
file_path: ${GITHUB_WORKSPACE}/test/src/build/HelloWorld.jar
- Directory where signed code object(s) will be written.
output_path: ${GITHUB_WORKSPACE}/artifacts
Inputs
- username: SSL.com account username. (Required)
- password: SSL.com account password (Required)
- credential_id: Credential ID for signing certificate. If credential_id is omitted and the user has only one eSigner code signing certificate, CodeSignTool will default to that. If the user has more than one code signing certificate, this parameter is mandatory. (Required)
- totp_secret: OAuth TOTP Secret. You can access detailed information on https://ssl.com/how-to/automate-esigner-ev-code-signing (Required)
- file_path: Path of code object to be signed. (Required)
- output_path: Directory where signed code object(s) will be written. If output_path is omitted, the file specified in -file_path will be overwritten with the signed file.
Java Code (Maven) JAR Signing Example Workflow
Prepare the components of the workflow
- Create a Github folder on your editor. Include workflows with the folder and create a yml file under the folder.

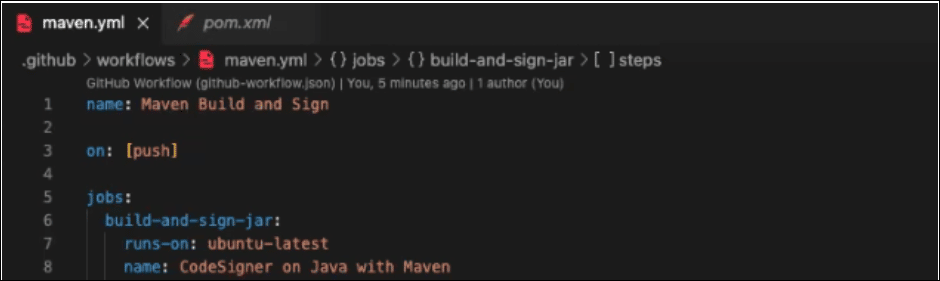
- Name your project and the type of workflow involved
Name: Maven Build and Sign
- Trigger this workflow on a push
on: push
- Create an environment variable
- Environment variables are used to make the samples more readable. In the screenshot above of the example workflow, the PROJECT_NAME, PROJECT_VERSION, and MAVEN_VERSION were optionally omitted. Signing can still proceed even with these omissions.
env: PROJECT_NAME: HelloWorld PROJECT_VERSION: 0.0.1 MAVEN_VERSION: 3.8.5 JAVA_VERSION: 17
- Define the jobs on your editor
jobs: build-and-sign-jar:
- Run job on Ubuntu Runner
runs-on: ubuntu-latest
- Create a name. When the workflow runs, this is the name that is logged.
name: CodeSigner on Java with Maven
Outline the steps for checking out the source code, setting up the Java and Maven environment, and creating Artifact Directory.
1) Check out the source code so that the workflow can access it.
steps: - uses: actions/checkout@v2

2) Set up the Java and Maven environment for the workflow to use.
- name: Install Maven and Java
uses: s4u/setup-maven-action@v1.3.1
with:
java-version: '${{env.JAVA_VERSION}}'
maven-version: '${{env.MAVEN_VERSION}}'
3) Create Artifact Directory to store signed and unsigned artifact files
- name: Create Directory
shell: bash
run: |
mkdir ${GITHUB_WORKSPACE}/artifacts
mkdir ${GITHUB_WORKSPACE}/packages
4) Build a maven project or solution and all of its dependencies.
After the jar file has been created, copy to ‘packages’ folder for signing
- In this written signing example workflow, multiple project types were created. This is why files of different project types were kept by creating subfolders. A subfolder named ‘java’ was created for Java projects. In the demo screenshot above, there was no need to create a subfolder named ‘java’ so this was not included in the script.
- name: Build Java Project
shell: bash
run: |
mvn clean install -f java/pom.xml
cp java/target/${{env.PROJECT_NAME}}-${{env.PROJECT_VERSION}}.jar ${GITHUB_WORKSPACE}/packages/${{env.PROJECT_NAME}}.jar
Outline the steps for the Sign and Upload jobs
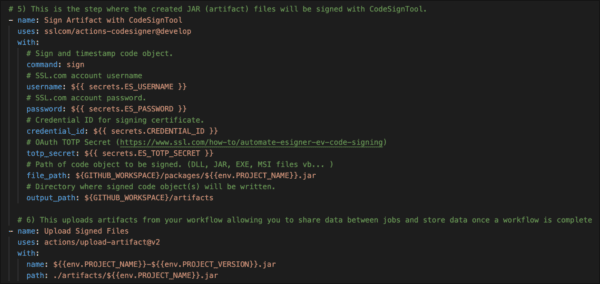
- The Sign job is the step where the created JAR (artifact) files will be signed with CodeSignTool.
- name: Sign Artifact uses: sslcom/actions-codesigner@develop with:
Sign and timestamp code object.
command: sign
SSL.com account username.
username: ${{secrets.ES_USERNAME}}
SSL.com account password.
password: ${{secrets.ES_PASSWORD}}
Credential ID for signing certificate.
credential_id: ${{secrets.CREDENTIAL_ID}}
OAuth TOTP Secret (https://ssl.com/how-to/automate-esigner-ev-code-signing)
totp_secret: ${{secrets.ES_TOTP_SECRET}}
Path of code object to be signed. (DLL, JAR, EXE, MSI files vb… )
file_path: ${GITHUB_WORKSPACE}/packages/${{env.PROJECT_NAME}}.jar
Directory where signed code object(s) will be written.
output_path: ${GITHUB_WORKSPACE}/artifacts
- The upload job is the step where artifacts from your workflow will be uploaded allowing you to share data between jobs and store data once a workflow is complete
- name: Upload Signed Files
uses: actions/upload-artifact@v2
with:
name: ${{env.PROJECT_NAME}}.jar
path: ./artifacts/${{env.PROJECT_NAME}}.jar
Get a build artifact uploader from Github Marketplace

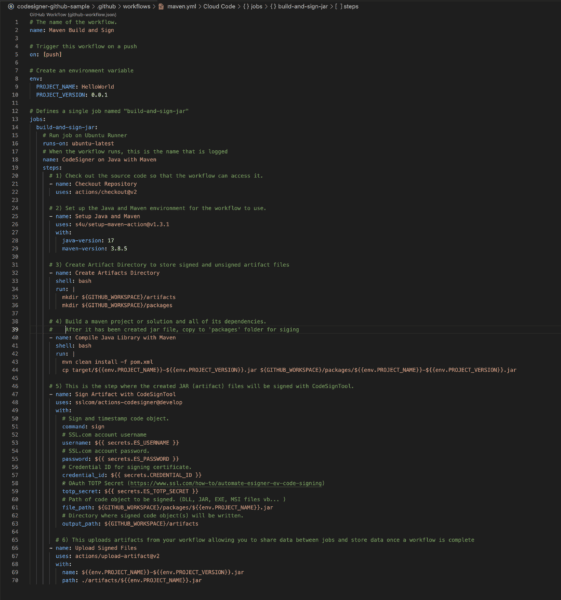
Review your coding script
Over-all the coding script for the buld, sign, and upload jobs should look like the image below. Make sure to correct any errors such as wrong spelling or erroneous line breaks in the script so that the signing process will run smoothly.
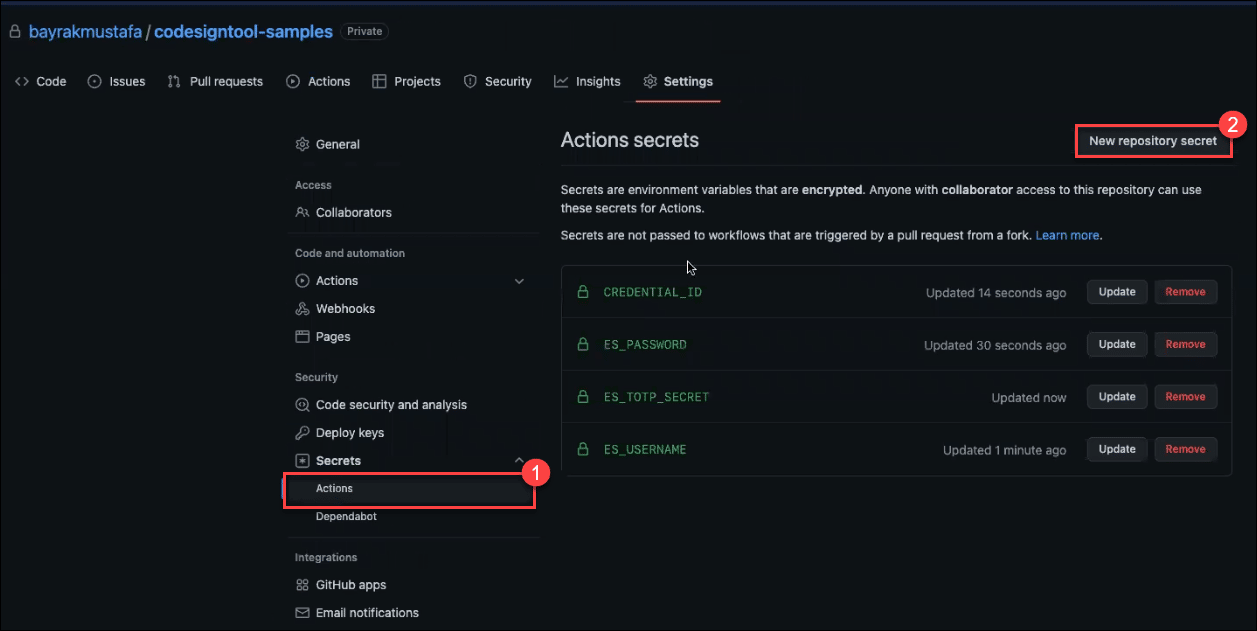
Define your Environment Variables
Go to the location of your project on your Github account. Click the Actions tab. Click the New repository secret button to place the values for each environment variable required in signing your code.
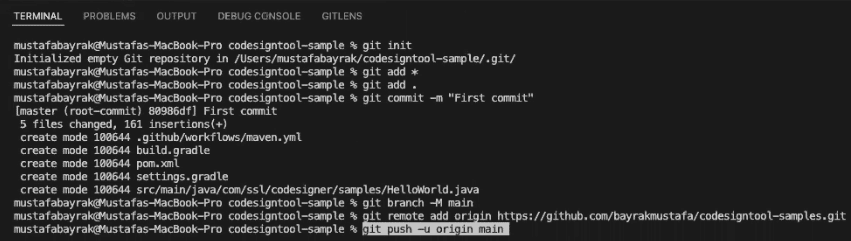
Create a new repository on the command line
Proceed to the location of your project on Github and copy each component of the push command.
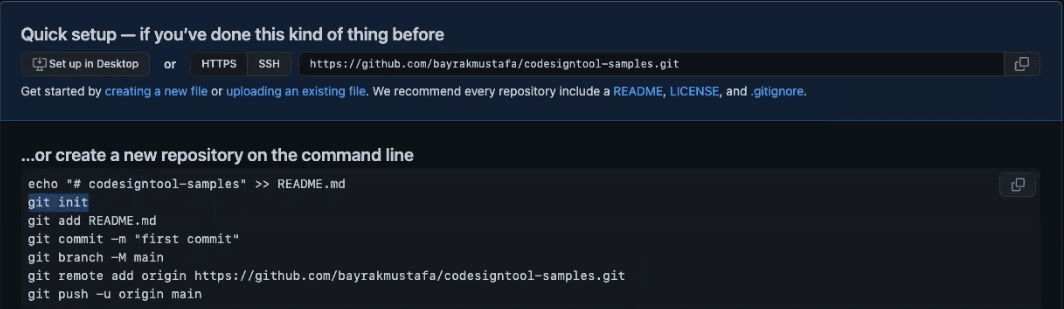
Push the project
Include each push command line in your code editor. Upon completion, the code will be automatically pushed on Github.
Wait for the artifact to be signed with eSigner CodeSignTool
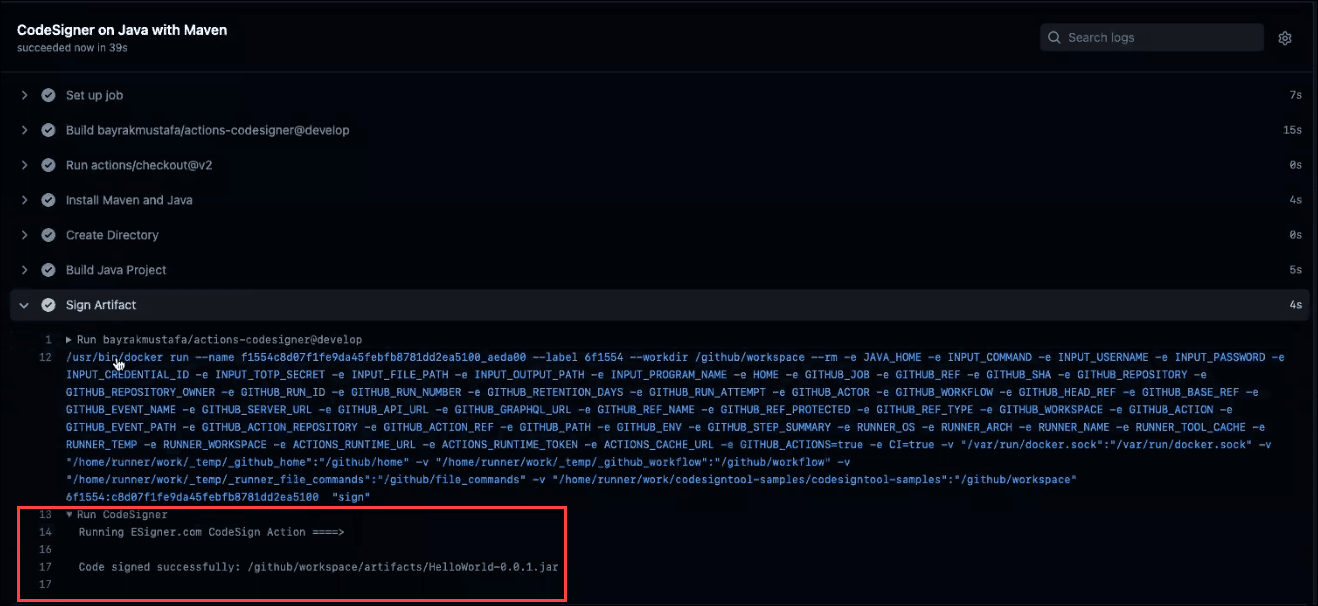
Upload the signed file
Click on the signed file to upload it.

Sample Github Actions Pipeline
Check out the sample Github Actions pipeline we have created on github.com/SSLcom/codesigner-github-sample
Other CI/CD Remote Signing Integration Guides
- Cloud Code Signing Integration with CircleCI
- Cloud Code Signing Integration with GitLab CI
- Cloud Code Signing Integration with Jenkins CI
- Cloud Code Signing Integration with Travis CI
- Cloud Code Signing Integration with Azure DevOps
- Cloud Code Signing Automation with CI/CD Services
Need Custom Solutions?
With our expert knowledge and five-star support staff, we’re ready and willing to work with you on custom solutions or enterprise-level high-volume signing discounts. Fill out the form below and we’ll be in touch.


